Thursday, December 15, 2005
True Cracks: Breaking 'Child Modeling' ring for fun and profit.
5:41AM-EST: the sky is dark and its wind is chilling. My servers are auricular; their fans are blazing through searing heat as my fingers pound away at keys, like a brigade of storming sun-tzu trained battalions vanishing and appearing causing visual deceit.
While in the midst of research, I noticed a rare message spring up across my terminal; "You have new unread mail!". Stunned, I executed "mail" and spotted the culprit: an email that has a blatantly false sender, a subject entirely in Brazilian, and a body full of JavaScript code refreshing itself so that a remote .scr (windows screen saver) file is executed.
"Hrm. Why would I randomly be sent this malicious email? Is this a direct attack? Is this just part of my email being harvested somewhere and being spammed?" I thought, before quickly visiting the web server hosting the possibly malicious file. It was determined that the server was located in Russia, and the web site in particular was an anarchist's revolutionary propaganda site.
5:46AM-EST: After translating the site, I used SearchMee.com's IP-Hunt and Whois.sc's Reverse-IP Lookup utilities' to determine if any other sites were hosted on the server.
At this point, my calm mood went into abstract disgust as it was realized that the hosts served on the same IP made reference to "Child Models". Before my imagination went too far of itself, I had to check out the sites myself.
5:58AM-EST: When I was able to calm down, concentrate, and think the situation through. I thought of reporting the site, but due to its very innocent looking front I knew it'd make more sense just to explore the system further. Remember that Brazilian email that brought me to this server in the first place? I took the full URL, excluding the windows screen saver file, and explored the listed files in the directory. There were several files, mostly images and such, but the one that caught my attention was "cmd.php".
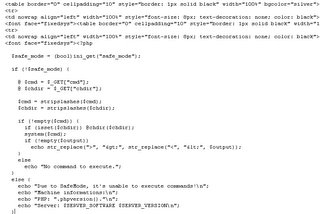
Executing the script yielded results, as it turned out to be a very simple piece of malicious PHP code for use in remote command execution. The code goes as follows: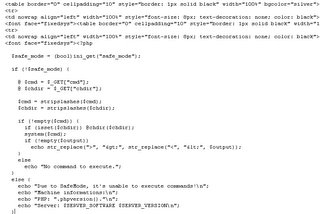
Before continuing, let me just emphasize a few facts. First, the vulnerability exploited by the spammer who sent me the original email, was in the PHP-Nuke distribution used on that anarchy revolutionists' site. Secondly, the attacker uploaded the cmd.php script, uploaded her malicious windows screen saver file, and did whatever she did from thereonin. Thirdly, the attacker left the server alone after I repeatedly deleted the malicious file she kept uploading.
6:09AM-EST: I executed a specially crafted reverse shell python code that connected back to a machine I have control of with shell command capability. I noticed I had nobody (99) UID, the server was running Fedora with SELinux secured kernel, and there weren't many SUID binaries on the server, neither were there many overwritable directories or files. I used the 'find' binary to search for all readable files on the server, and the lengthy process proved useless. Permissions throughout the server were tight, though I could read the public_html per user. I managed to discover the primary site of the server, which sold "tokens" to the "model" sites. You could only access the sites' member sections after creating a user account, from the token page located at the primary site.
6:49AM-EST: Since I had a shell with apache privileges, I was able to read the .htaccess, .htpasswd, ttlog.txt (account creation/deletion with plaintext passwords), and configuration files for each site. That proved to be useful, for I was able to dump the entire database containing client email addresses, their passwords, and e-gold identification number -- thanks to the configurations within each site.
... To be continued.
the following post is the start of a series of stories portraying actual, possible, or fictional penetrations. The post titles will be prefixed with "True Cracks:", and will pertain to keywords specified in its suffix. Enjoy!TARGET: Child Porn ring "childmodel.ru"
5:41AM-EST: the sky is dark and its wind is chilling. My servers are auricular; their fans are blazing through searing heat as my fingers pound away at keys, like a brigade of storming sun-tzu trained battalions vanishing and appearing causing visual deceit.
While in the midst of research, I noticed a rare message spring up across my terminal; "You have new unread mail!". Stunned, I executed "mail" and spotted the culprit: an email that has a blatantly false sender, a subject entirely in Brazilian, and a body full of JavaScript code refreshing itself so that a remote .scr (windows screen saver) file is executed.
"Hrm. Why would I randomly be sent this malicious email? Is this a direct attack? Is this just part of my email being harvested somewhere and being spammed?" I thought, before quickly visiting the web server hosting the possibly malicious file. It was determined that the server was located in Russia, and the web site in particular was an anarchist's revolutionary propaganda site.
5:46AM-EST: After translating the site, I used SearchMee.com's IP-Hunt and Whois.sc's Reverse-IP Lookup utilities' to determine if any other sites were hosted on the server.
At this point, my calm mood went into abstract disgust as it was realized that the hosts served on the same IP made reference to "Child Models". Before my imagination went too far of itself, I had to check out the sites myself.
"Child Models" is but one of the terms used loosely by Pedophiles who share pictures of barely-clothed children in sexual positions.While visiting the sites, it was quickly realized that they were in fact linked to suggestive pornography involving children.
5:58AM-EST: When I was able to calm down, concentrate, and think the situation through. I thought of reporting the site, but due to its very innocent looking front I knew it'd make more sense just to explore the system further. Remember that Brazilian email that brought me to this server in the first place? I took the full URL, excluding the windows screen saver file, and explored the listed files in the directory. There were several files, mostly images and such, but the one that caught my attention was "cmd.php".

Executing the script yielded results, as it turned out to be a very simple piece of malicious PHP code for use in remote command execution. The code goes as follows:
Before continuing, let me just emphasize a few facts. First, the vulnerability exploited by the spammer who sent me the original email, was in the PHP-Nuke distribution used on that anarchy revolutionists' site. Secondly, the attacker uploaded the cmd.php script, uploaded her malicious windows screen saver file, and did whatever she did from thereonin. Thirdly, the attacker left the server alone after I repeatedly deleted the malicious file she kept uploading.
6:09AM-EST: I executed a specially crafted reverse shell python code that connected back to a machine I have control of with shell command capability. I noticed I had nobody (99) UID, the server was running Fedora with SELinux secured kernel, and there weren't many SUID binaries on the server, neither were there many overwritable directories or files. I used the 'find' binary to search for all readable files on the server, and the lengthy process proved useless. Permissions throughout the server were tight, though I could read the public_html per user. I managed to discover the primary site of the server, which sold "tokens" to the "model" sites. You could only access the sites' member sections after creating a user account, from the token page located at the primary site.
6:49AM-EST: Since I had a shell with apache privileges, I was able to read the .htaccess, .htpasswd, ttlog.txt (account creation/deletion with plaintext passwords), and configuration files for each site. That proved to be useful, for I was able to dump the entire database containing client email addresses, their passwords, and e-gold identification number -- thanks to the configurations within each site.
... To be continued.